Thème Réseau et sécurité
Présentation
- La conception de protocoles de communicationes réseaux de communicationcouvrnt à la fois les technologies de courte et longue portée. Parmi les problématiques explorées, l’allocation des ressources et la gestion d’interférences dans des réseaux LoRaWAN, Wi-Fi, cellulaires et satellitaires, ainsi que l’interopérabilité entre différentes technologies de réseau, visant à créer des infrastructures de communication plus robustes et flexibles. L’optimisation dynamique des performances des réseaux devient de plus en plus cruciale avec la complexification et la densification des réseaux. Dans ce contexte, une partie de nos solutions repose sur es modèles d’Intelligence Artificielle (IA) qui permettent d’optimiser dynamiquement les performances des réseaux, en améliorant la gestion des ressources et en réduisant les interférences. Ces contributions s'adaptent aux besoins des applications allant de la surveillance environnementale aux cas d'usage industriels.
 |
 |
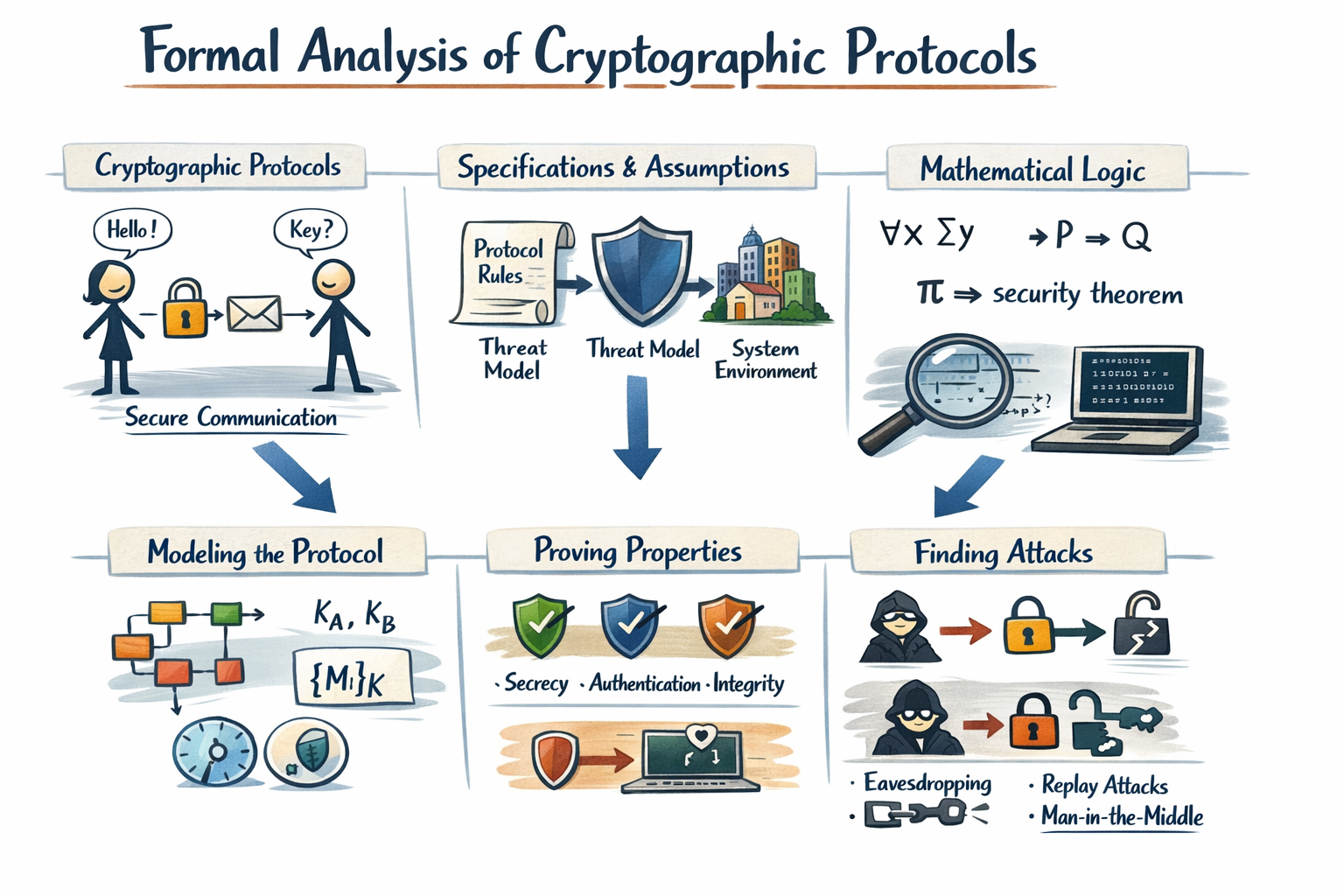
- La sécurisation P
 |
 |
Enfin, en outre ces trois activités structurantes, le thème RS entretient également plusieurs travaux connexes et en collaboration avec d'autres équipes et structures de recherche. Dans le cadre d'une collaboration avec l'Institut Pascal, nous travaillons sur l'implémentation de réseaux de neurones profonds sur des architectures FPGA. Ces travaux impliquent une forte dimension d'optimisation à la fois en termes de performances, mais également en termes d'espace pris sur le FPGA. Un second axe de recherche se focalise sur la sécurité des architectures LLM complexes (impliquant des pipelines RAG, des agents et du fine-tuning) dans le cadre d'une collaboration inter-thèmes avec le thème DSI de l'axe SIC. Cette collaboration est structurée autour de la Chaire Mécénale Utilisation Fiable et de Confiance des LLMs. Enfin, un troisième axe s'intéresse aux preuves à divulgation nulle de connaissance (zero-knowledge proofs) basées sur des objets physiques (jeux de cartes, balances de Roberval). Ces activités en collaboration avec l'Université Electro-Technique de Tokyo au Japon permettent d'agir en complément des primitives cryptographiques dans des environnements où l'informatique n'est pas considérée, tels que les élections avec urne et bulletins.
Nous organisons un séminaire mensuel : https://sancy.iut.uca.fr/~durand/seminaire/
Actualités
Dernières Publications
Distributed Frame Deduplication Mechanism for Mobile LoRaWAN Network
IEEE VTC Spring
Osama Allabwani, Olivier Blazy, Pascal Lafourcade, Charles Olivier-Anclin, Olivier Raynaud - 1 juin 2026
Sanitizable Signatures with Different Admissibility Policies for Multiple Sanitizers
ACM Asia Conference on Computer and Communications Security (ASIA CCS '26)
Quentin Bramas, Stéphane Devismes, Anaïs Durand, Pascal Lafourcade, Anissa Lamani - 1 juin 2026
77 nuances de couleurs
ALGOTEL 2026 — 28es Rencontres Francophones sur les Aspects Algorithmiques des Télécommunications
Karine Altisen, Anaïs Durand, Pascal Lafourcade, Oussama Nahnah - 1 juin 2026
Eviter un obstacle avec des robots lumineux : synthèse d'algorithmes
ALGOTEL 2026 — 28es Rencontres Francophones sur les Aspects Algorithmiques des Télécommunications
Carlos Fernandez Hernandez, Christelle Caillouet, Alexandre Guitton, Oana Iova, Fabrice Valois - 1 juin 2026
Parler, c'est bien... répondre, c'est mieux : le trafic descendant dans LoRaWAN
CORES 2026 — 11es Rencontres Francophones sur la Conception de Protocoles, l'Évaluation de Performances et l'Expérimentation des Réseaux de Communication
Jannik Dreier, Pascal Lafourcade, Yliès Falcone, Gabriele Lenzini - 27 avril 2026
Secure and Verifiable Test and Assessment System project DMP
Quentin Bramas, Stéphane Devismes, Anaïs Durand, Pascal Lafourcade, Anissa Lamani - 14 janvier 2026
77 Shades of Grey
Gwendoline Hochet Derévianckine, Alexandre Guitton, Oana Iova, Baozhu Ning, Fabrice Valois - 19 novembre 2025
Hate or Love in the 2.4 GHz ISM band: The Story of LoRa® and IEEE 802.11g
ACM Transactions on Internet of Things
Mariem Zayene, Oussama Habachi, Gérard Chalhoub - 18 novembre 2025
Toward hyper-adaptive AI-enabled 6G networks for energy efficiency: techniques, classifications and tradeoffs
Zoé Lagache, Pierre-Henri Thevenon, Maxime Puys, Oum-El-Kheir Aktouf - 12 novembre 2025
Dissecting Mirai : Spatio-Sequential Analysis and Restoration Strategies Using MITRE ATT&CK and D3FEND
30th Nordic Conference on Secure IT Systems (NordSec)
Toutes les publis se trouvent ici
Projets
Equipe
Responsables
Enseignants-Chercheurs
- BATTA Mohamed
- BU Gewu
- CHALHOUB Gérard
- DELOBEL François
- DE VAULX Christophe
- DURAND Anaïs
- EL RACHKIDY Nancy
- FREITAS Antonio
- GUITTON Alexandre
- HABACHI Oussama
- LAFOURCADE Pascal
- LI Jian-Jin
- MESNARD Emmanuel
- MIGDAL Denis
- OLIVIER-ANCLIN Charles
- PUYS Maxime
Professeurs émérites
Post-docs
Doctorants
- ADJE Karidja Dominique
- ALLABWANI Osama
- CHAGNON Dorine
- DURECU Florent
- ESSAFI Ayoub
- MUKUND Shrey
- NAHNAH Oussama
- NAMA NYAM Guy Anthony
- NOUYEP NOUNDJIO Steve Durand
- ZHAO Yan